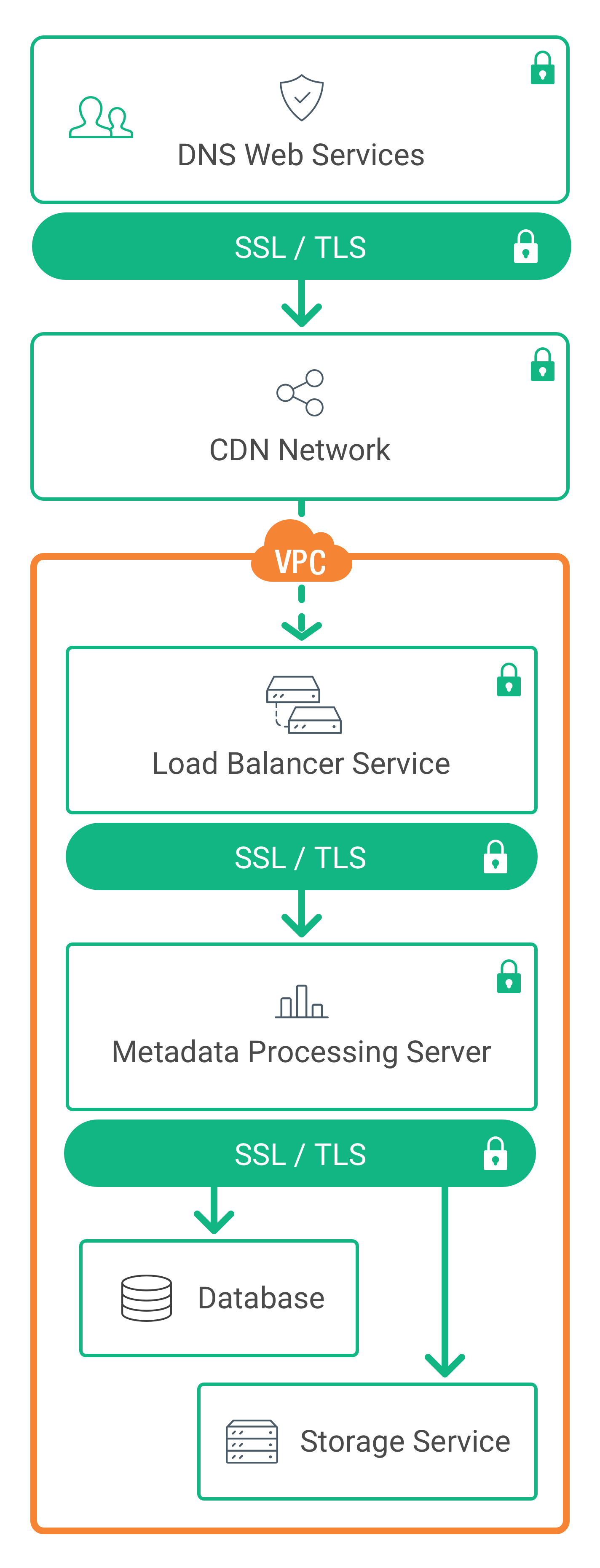
WorkLink 系統帳號認證採用業界標準機制 OAuth 2.0 登入驗證及授權協定,資料傳輸過程以私有安全網段配合 SSL/TLS 等資訊安全協議加密,完善管理伺服器與資料庫,為企業客戶資料建構最完整的防護。
最用心的防護,最安心的服務。
WorkLink 系統服務架構採用全球最大雲端運算服務提供商-企業級亞馬遜網路服務系統(Amazon Web Services, AWS),支援動態負載平衡及備援管理,隨時可依流量變化彈性部署硬體資源,搭配動態快取服務及動態儲存裝置,確保應用服務持續不中斷。
嚴格安全控管機制
採用群組隔離分層級管控之安全架構,所有操作皆有紀錄可追蹤與檢驗,確保系統平台安全。
加密傳輸處理
傳輸皆使用 SSL / TLS 1.2 保護資料傳輸,並且透過金鑰與高階加密標準(AES)建置安全傳輸管道。
單一裝置登入
同時間單一帳號只允許登入單一裝置。此機制提供高度安全保障,確保連接之服務資訊一致,而非由他人假冒。
網路傳輸高速低延遲
採用全球內容交付網路(CDN)服務架構,透過高效能內部骨幹網路與各國 ISP 直接連接,降低網路延遲。
OAuth 2.0 資源保護
採用標準 OAuth 2.0 機制進行存取資源保護,使用者必須進行身份驗證並取得有效 Token 才可進行檔案存取。
跨國即時備份機制
資料即時儲存至多個跨國地理位置之實體設施進行異地備援,並自動將檔案即時異地備援至位於另外一國家區域資料中心,提供使用者最佳檔案耐久性。
多層防護分散式容錯架構
採用多層群組相互隔離之分散式容錯架構,提供客戶安全可靠數據傳輸與資料儲存服務。雲端伺服器擁有獨立電源、空調、網路環境,且橫跨多個資料中心,並實施 24 小時監視機制。
資安架構圖
開始讓工作更有效率

全功能 15 天免費試用





